A variant of the Mirai botnet is targeting almost two dozen vulnerabilities aiming to take control of D-Link, Arris, Zyxel, TP-Link, Tenda, Netgear, and MediaTek devices to use them for distributed denial-of-service (DDoS) attacks.
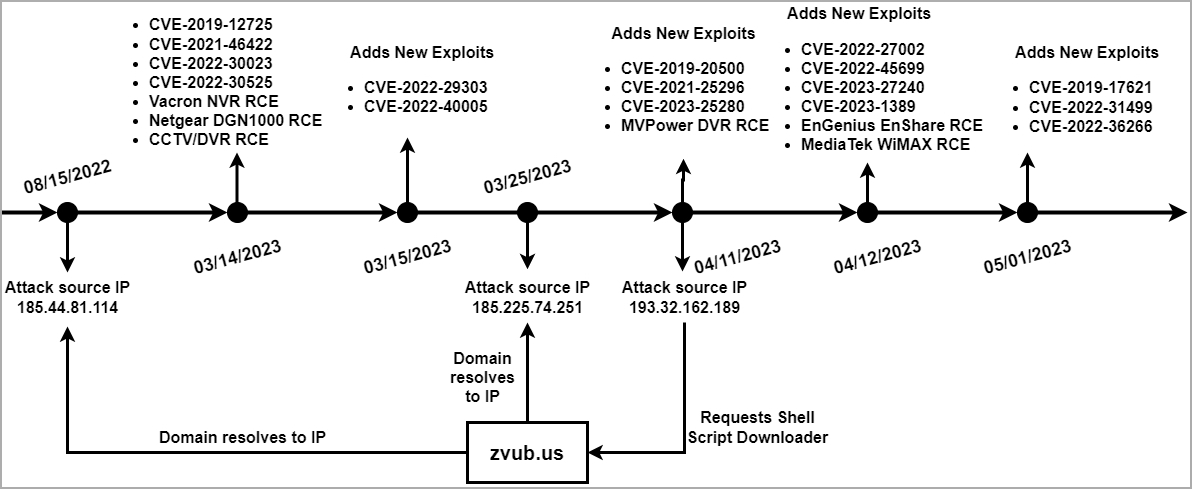
The malware has been identified by Unit 42 researchers of Palo Alto Networks in two ongoing campaigns that started on March 14 and spiked in April and June.
In a report today, the researchers warn that the botnet developers continue to add code for exploitable vulnerabilities.
In total, the malware targets no less than 22 known seccurity issues in various connected products, which include routers, DVRs, NVRs, WiFi communication dongles, thermal monitoring systems, access control systems, and solar power generation monitors.
Below is the complete list of the vulnerabilities and products targeted by the malware in the latest version that Unit 42 researchers identified:

One of these flaws, CVE-2023-1389, affects the TP-Link Archer A21 (AX1800) WiFi router and it was reported by ZDI as being exploitated from Mirai malware since late April. However, it is unclear if the two refer to the same activity.
Attack details
The attack begins with exploiting one of the mentioned flaws, laying the ground for executing a shell script from an external resource.
This script will download the botnet client that matches the architecture of the compromised device, covering armv4l, arm5l, arm6l, arm7l, mips, mipsel, sh4, x86_64, i686, i586, arc, m68k, and sparc.
After the bot client executes, the shell script downloader deletes the client’s file to sweep infection tracks and to reduce the likelihood of detection.
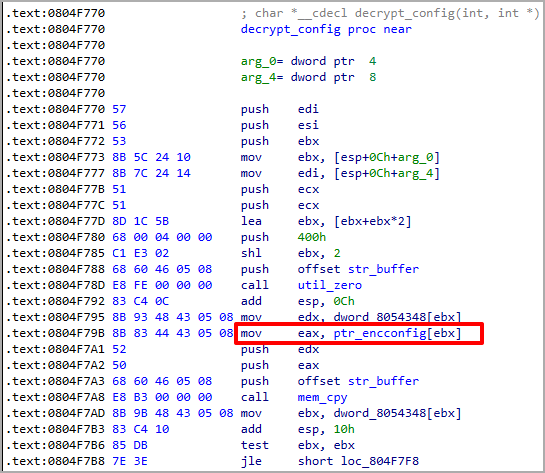
Compared to standard Mirai variants in circulation, this one directly accesses the encrypted strings in the .rodata section through an index instead of setting up a string table to get the botnet client’s configuration.
This approach bypasses the encrypted string table initialization, giving the malware speed and stealthiness and making it less likely to be detected by security tools.
Unit 42 also notes that this Mirai variant does not have the capacity to brute force telnet/SSH login credentials, so its distribution relies entirely on operators manually exploiting the vulnerabilities.
Lowering the risk of infection is possible by applying the latest firmware update available from the device vendor or maker, switch from the default access credentials to something strong and unique, and remove remote admin panel accessibility if not needed.
Signs of botnet malware infection on an IoT device may include excessive overheating, change of settings/configuration, frequent disconnections, and an overall drop in performance.
Update 6/26: D-Link recommends replacing the models impacted by this campaign, as they have reached their end-of-life, and will not be getting a fixing update for the exploited vulnerabilities.



Comments
DLINKSIRT - 10 months ago
For owners of EOL/EOS products, please contact shop.us.dlink.com they will provide a significant discount to an updated WiFi6 router that receives updates and is developed under strict IEC62443 Life-Cycle security audited development.
DNS-320 Legacy Site EOL/EOS 12/1/2018
https://legacy.us.dlink.com/pages/product.aspx?id=5182449a065f43329cc66a09d43b1c79
The resources associated with these products have ceased their development and are no longer supported.
D-Link Systems, Inc. recommends retiring these products and replacing them with products that receive firmware updates.
Publiic Announcement: https://supportannouncement.us.dlink.com/announcement/publication.aspx?name=SAP10183
DIR-820L Legacy Site: EOL/EOS 11/17
https://legacy.us.dlink.com/pages/product.aspx?id=00c2150966b046b58ba95d8ae3a8f73d
The resources associated with these products have ceased their development and are no longer supported. D-Link Systems, Inc. recommends retiring these products and replacing them with products that receive firmware updates.
DIR-859 Legacy Site EOL/EOS 12/10/2020
https://legacy.us.dlink.com/pages/product.aspx?id=a64612142a3041d98642960e5f840fb6
The resources associated with these products have ceased their development and are no longer supported. D-Link Systems, Inc. recommends retiring these products and replacing them with products that receive firmware updates.
DWL-2600AP:
Announcement with Fix: https://supportsiteadmin.dlink.com/supportarticle/supportarticle.aspx?article=4D252F2594214AEAA981ADD42F7DA1A4
And there is a newer hotfix patch for additional disclosures since 2019: https://support.dlink.com/ProductInfo.aspx?m=DWL-2600AP
Regards,
security _ at_ dlink _d0t_ com