Microsoft has released a Chrome extension named "Windows Defender Browser Protection" that ports Windows Defender's —and inherently Edge's— anti-phishing technology to Google Chrome.
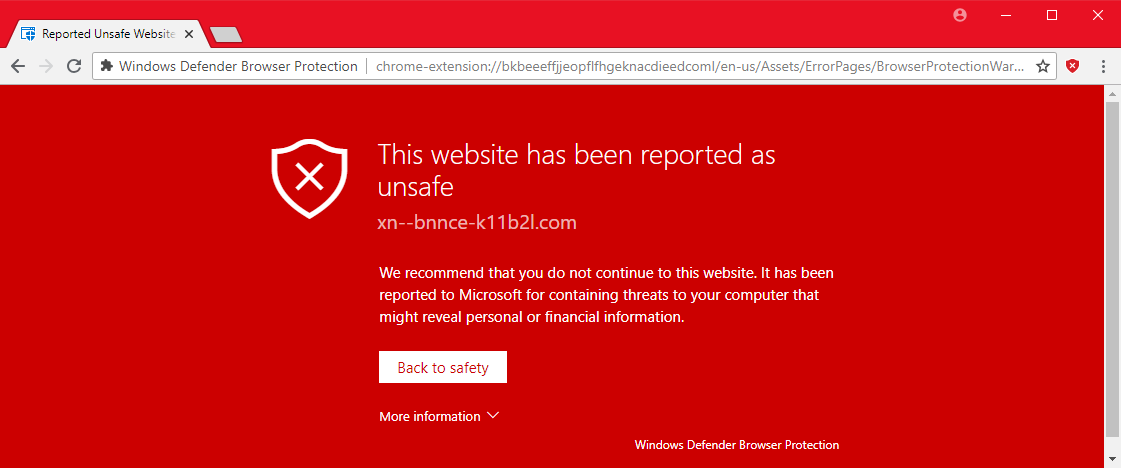
The extension works by showing bright red-colored pages whenever users are tricked into accessing malicious links.
The warnings are eerily similar to the ones that Chrome natively shows via the Safe Browsing API, but are powered by Microsoft's database of malicious links —also known as the SmartScreen API.
Chrome users should be genuinely happy that they can now use both APIs for detecting phishing and malware-hosting URLs. The SmartScreen API isn't as known as Google's more famous Safe Browsing API, but works in the same way, and possibly even better.
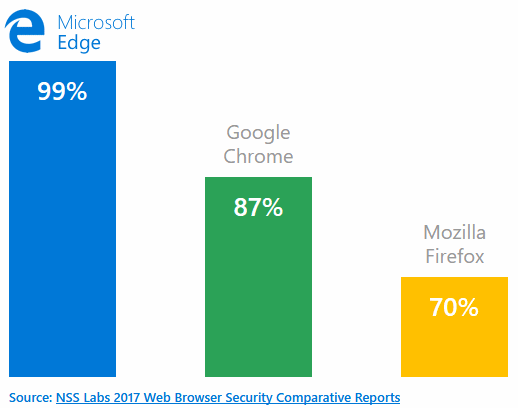
An NSS Labs benchmark revealed that Edge (with its SmartScreen API) caught 99 percent of all phishing URLs thrown at it during a test last year, while Chrome only detected 87 percent of the malicious links users accessed.
Microsoft made a mistake in releasing Edge in an unfinished state in 2015, but the browser has quietly turned into a solid product, especially when it comes to security features.
The SmartScreen API is a trustworthy technology, and the anti-exploit protection Edge benefits due to its close integration with Windows 10 make it a hard nut to crack when it comes to web-based attacks.
It's unclear why Microsoft chose to port SmartScreen to Google Chrome, but we're glad they did it.


Comments
ken4bleepingcomputer - 6 years ago
NSS Labs should learn that a bar graph has bars that are proportional to the quantities being represented. Plotting the percentage from zero will make a whole different picture. I wonder if Microsoft paid for this study.
ken4bleepingcomputer - 6 years ago
I now see that the Microsoft link in the article (https://browserprotection.microsoft.com/learn.html) takes me to a page with a correct bar graph. Maybe BleepingComputer's editors cropped this picture down to size.
campuscodi - 6 years ago
It's a responsive chart. That's how it appeared when I took a screenshot of it.