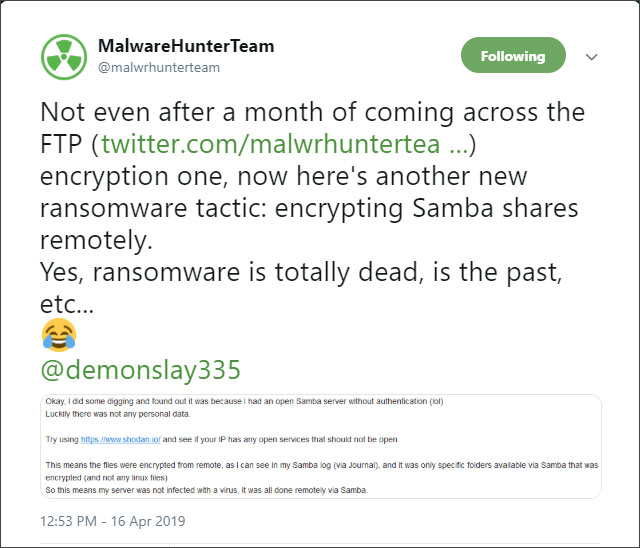
A new ransomware family called NamPoHyu Virus or MegaLocker Virus is targeting victims a bit differently than other ransomware. Instead of an executable running on a victim's computer, the attacker is running the ransomware locally and having it remotely encrypt accessible Samba servers.
Ransomware infections are typically installed on the computer that will be encrypted, whether that be through other malware, malicious email attachments, or by the attackers hacking a computer or network.
This new ransomware is doing things differently by searching for accessible Samba servers, brute forcing the passwords, and then remotely encrypting their files and creating ransom notes.
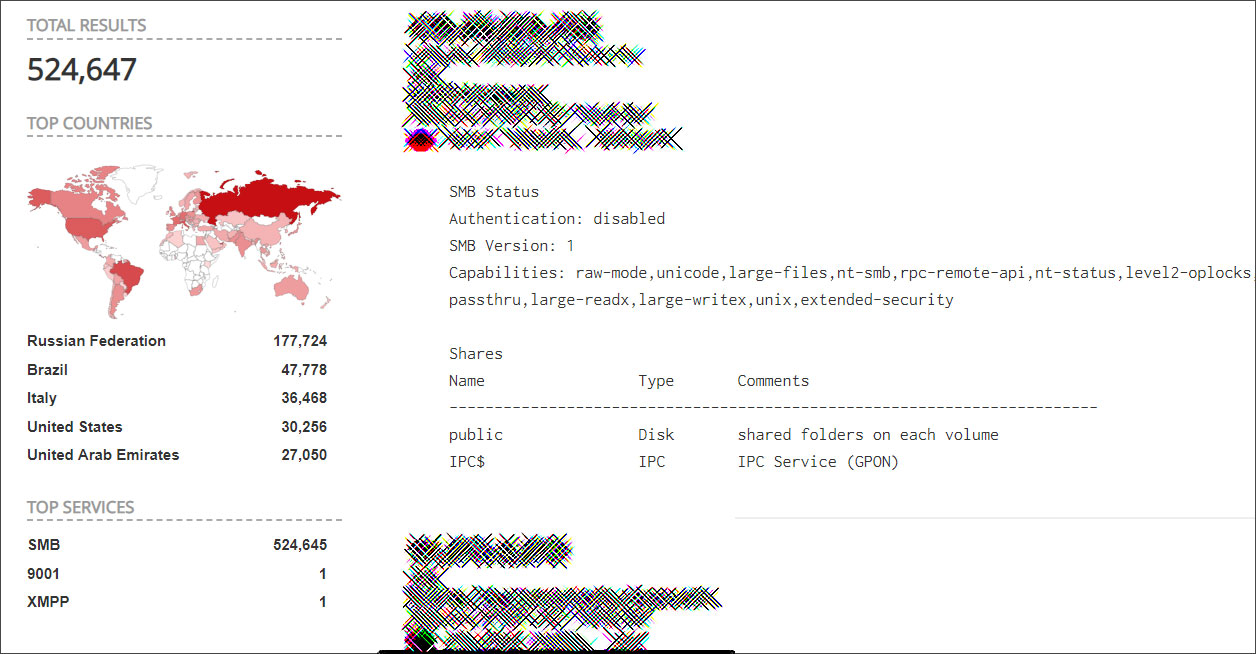
Unfortunately, there are plenty of targets, as Shodan shows close to 500,000 accessible Samba servers.
The good news is that a method to decrypt files encrypted by this ransomware may have been discovered. This article will be updated as more information becomes available, so you can register an account and subscribe to the article's comments or subscribe to the MegaLocker NamPoHyu Virus Support & Help topic in the forums
MegaLocker Virus first spotted in March 2019
Reports of this ransomware first started in March 2019, where users stated that their NAS storage devices were suddenly encrypted by a ransomware called MegaLocker Virus.
This ransomware would append the .crypted extension to encrypted files and create ransom notes named !DECRYPT_INSTRUCTION.TXT.
This ransom note contained instructions to contact alexshkipper@mail.ru and send a photo of the victim at a birthday, holiday, hobbies or some other personal event. If you could prove you were private person the ransom amount would be $250 USD, otherwise it would be $1,000 for companies
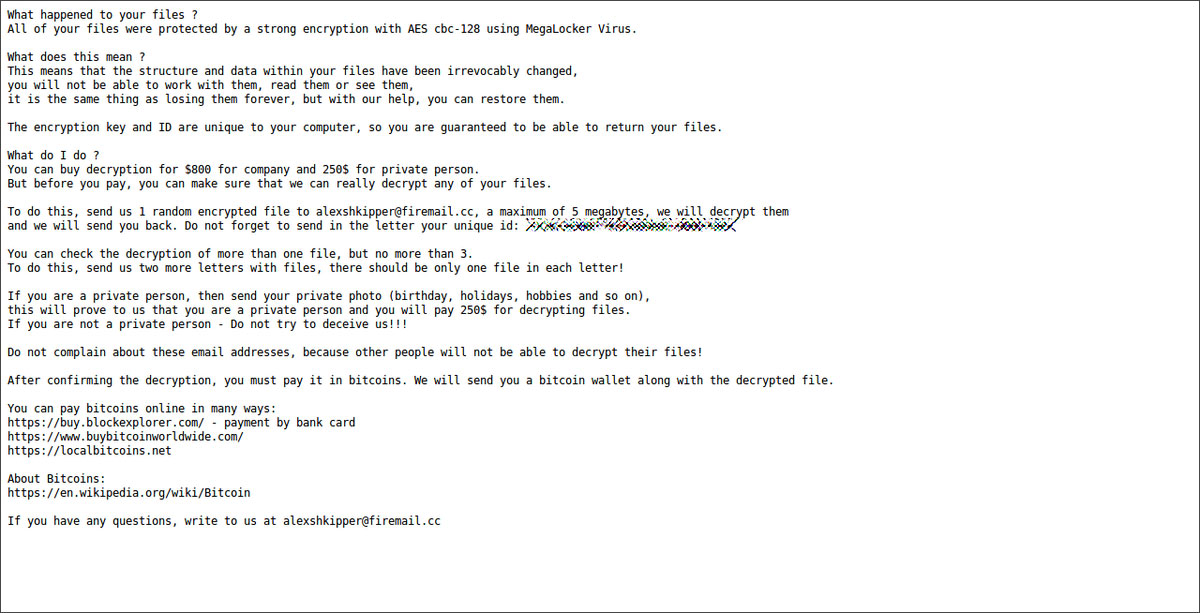
While one report states they feel they were infected through FTP, as most of the victims at this time were NAS devices, I am leaning towards encryption being done via Samba.
Changed to NamPoHyu Virus in April
In early April 2019, users began reporting on BleepingComputer that the ransomware switched its name to the NamPoHyu Virus and started appending the .NamPoHyu extension to encrypted files.
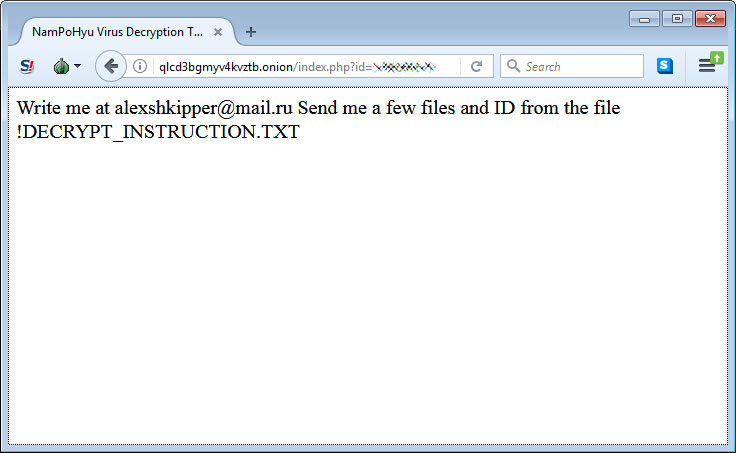
While the ransom note filename stayed the same, the instructions now included a link to a Tor payment site.
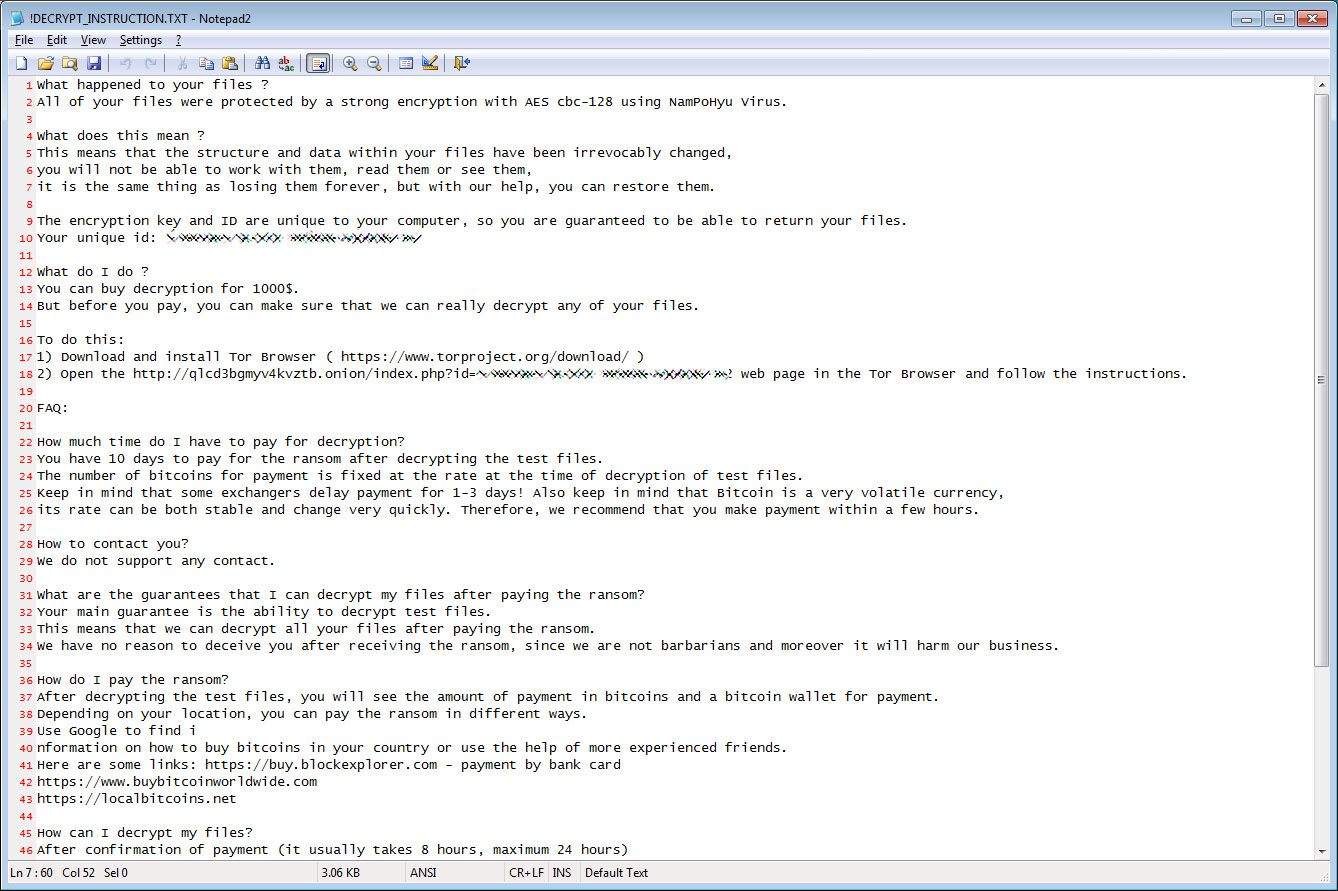
When going to the Tor site, victims are told to email alexshkipper@firemail.cc with the ID listed in the ransom note for payment instructions.
The ransom amounts appear to have stayed the same, with $250 for personal victims and $1,000 USD in bitcoins for companies.
As previously stated, we believe there may be a way to decrypt these files, so please check back here for updates or ask in our MegaLocker NamPoHyu Virus Support & Help topic.
How to protect yourself from Ransomware
In order to protect yourself from ransomware it is important that you use good computing habits and security software. The most important step is to always have a reliable and tested backup of your data that can be restored in the case of an emergency, such as a ransomware attack.
You should also make sure that you do not have any computers running remote desktop services connected directly to the Internet. Instead place computers running remote desktop behind VPNs so that they are only accessible to those who have VPN accounts on your network.
With MegaLocker and NamPoHyu, we also now know that we need to make sure services such as FTP or Samba are protected by strong passwords and preferrably not exposed to the Internet at all.
A good security software solution that incorporates behavioral detections to combat ransomware and not just use signature detections or heuristics is important as well. For example, Emsisoft Anti-Malware and Malwarebytes Anti-Malware both contain behavioral detection that can prevent many, if not most, ransomware infections from encrypting a computer.
Last, but not least, make sure you practice the following security habits, which in many cases are the most important steps of all:
- Backup, Backup, Backup!
- Do not open attachments if you do not know who sent them.
- Do not open attachments until you confirm that the person actually sent you them,
- Scan attachments with tools like VirusTotal.
- Do not connect Remote Desktop Services directly to the Internet. Instead, make sure they can only be accessed by logging into a VPN first.
- Make sure all Windows updates are installed as soon as they come out! Also make sure you update all programs, especially Java, Flash, and Adobe Reader. Older programs contain security vulnerabilities that are commonly exploited by malware distributors. Therefore it is important to keep them updated.
- Make sure you use have some sort of security software installed that uses behavioral detections or white list technology. White listing can be a pain to train, but if your willing to stock with it, could have the biggest payoffs.
- Use hard passwords and never reuse the same password at multiple sites.
- BACKUP!
For a complete guide on ransomware protection, you visit our How to Protect and Harden a Computer against Ransomware article.
Update 4/16/19 7:08 PM EST: Strike that! The folks at Shodan provided an updated query that shows there are over 500,000 publicly accessible Samba servers.
IOCs:
Associated Sites:
http://qlcd3bgmyv4kvztb.onion
Associated email addresses:
alexshkipper@mail.ru
alexshkipper@firemail.cc
Ransom note text:
What happened to your files ?
All of your files were protected by a strong encryption with AES cbc-128 using NamPoHyu Virus.
What does this mean ?
This means that the structure and data within your files have been irrevocably changed,
you will not be able to work with them, read them or see them,
it is the same thing as losing them forever, but with our help, you can restore them.
The encryption key and ID are unique to your computer, so you are guaranteed to be able to return your files.
Your unique id: [id]
What do I do ?
You can buy decryption for 1000$.
But before you pay, you can make sure that we can really decrypt any of your files.
To do this:
1) Download and install Tor Browser ( https://www.torproject.org/download/ )
2) Open the http://qlcd3bgmyv4kvztb.onion/index.php?id=[id] web page in the Tor Browser and follow the instructions.
FAQ:
How much time do I have to pay for decryption?
You have 10 days to pay for the ransom after decrypting the test files.
The number of bitcoins for payment is fixed at the rate at the time of decryption of test files.
Keep in mind that some exchangers delay payment for 1-3 days! Also keep in mind that Bitcoin is a very volatile currency,
its rate can be both stable and change very quickly. Therefore, we recommend that you make payment within a few hours.
How to contact you?
We do not support any contact.
What are the guarantees that I can decrypt my files after paying the ransom?
Your main guarantee is the ability to decrypt test files.
This means that we can decrypt all your files after paying the ransom.
We have no reason to deceive you after receiving the ransom, since we are not barbarians and moreover it will harm our business.
How do I pay the ransom?
After decrypting the test files, you will see the amount of payment in bitcoins and a bitcoin wallet for payment.
Depending on your location, you can pay the ransom in different ways.
Use Google to find i
nformation on how to buy bitcoins in your country or use the help of more experienced friends.
Here are some links: https://buy.blockexplorer.com - payment by bank card
https://www.buybitcoinworldwide.com
https://localbitcoins.net
How can I decrypt my files?
After confirmation of payment (it usually takes 8 hours, maximum 24 hours)
you will see on this page ( http://qlcd3bgmyv4kvztb.onion/index.php?id=[id] ) a link to download the decryptor and your aes-key
(for this, simply re-enter (refresh) this page a day after payment)
Download the program and run it.
Attention! Disable all anti-virus programs, they can block the work of the decoder!
Copy aes-key to the appropriate field and select the folder to decrypt.
The program will scan and decrypt all encrypted files in the selected folder and its subfolders.
We recommend that you first create a test folder and copy several encrypted files into it to verify the decryption.
About Bitcoins:
https://en.wikipedia.org/wiki/Bitcoin
About Tor Browser:
https://www.torproject.org


Comments
Raztro - 5 years ago
Thank you for all the information. It's somewhat reliefing to hear how they possibly got in. Again thank you.
Emmanuel_ADC-Soft - 4 years ago
Dr.Web may decrypt some variants of this new .NamPoHyu extension crypted files.
To confirm if we are able to calculate the decryption key we need the ransom note file !DECRYPT_INSTRUCTION.TXT and 3-4 crypted files.
Opening a request at Dr.Web is free of charge but they will request fees if they are able to build a decryptor to get back your files.
After reviewing the data provided and only if decryption is possible, you will be offered to buy Dr.Web Rescue Pack for 150 Euro.
It includes decryption services and a Dr.Web Security Space license for 1 PC / 2 years.
For any request about this MegaLocker ransomware, you can contact me at emte@adc-soft.com as Dr.Web's official partner.
Kind regards,
Emmanuel
--
ADC-Soft - emte@adc-soft.com
18bis, rue de l’Est – 92100 Boulogne-Billancourt (France)
Lawrence Abrams - 4 years ago
Noone should pay anyone for decryption on this ransomware, including to Dr. Web.
Emmanuel_ADC-Soft - 4 years ago
"Noone should pay anyone for decryption on this ransomware, including to Dr. Web."
Hello,
Is there any free tool to decrypt this ransomware ?
Can you give more informations please how to decrypt these crypted files without any fees (For informations there is no free decryptor at Dr.Web, request are free but they always ask for purchasing Dr.Web rescue Pack if they are able to decrypt the files).
Thank you in advance.
Kind regards,
Emmanuel
stromdriver - 4 years ago
hope the decryption releases soon, i got hit with this when no one was even home, and my router auto blocks login attempt sources after a few tries, 'lost' our vacation footage from last fall, everything else on the drive was replaceable (or just backups of other machines)