
A security researcher has found a method that can be used to easily identify the public IP addresses of misconfigured dark web servers. While some feel that this researcher is attacking Tor or other similar networks, in reality he is exposing the pitfalls of not knowing how to properly configure a hidden service.
One of the main purposes of setting up a dark web web site on Tor is to make it difficult to identify the owner of the site. In order to properly anonymize a dark web site, though, the administrator must configure the web server properly so that it is only listens on localhost (127.0.0.1) and not on an IP address that is publicly exposed to the Internet.
Yonathan Klijnsma, a threat researcher lead for RiskIQ, has discovered that there are many Tor sites that utilize SSL certificates and also misconfigure a hidden service so that it is accessible via the Internet. As RiskIQ crawls the web and associates any SSL certificate it discovers to it's hosted IP address, it was easy for Klijnsma to map a misconfigured hidden Tor service with its corresponding public IP address.
"The way these guys are messing up is that they have their local Apache or Nginx server listening on any (* or 0.0.0.0) IP address, which means Tor connections will work obviously, but also external connections will as well," Klijnsma told BleepingComputer. "This is especially true if they don't use a firewall. These servers should be configured to only listen on 127.0.0.1."
When asked how often he sees misconfigured servers that expose their public IP address, he told us that it is quite common.
"Continuously. I'm not even kidding. Some don't listen on http/https, so I don't know what they are, but they have onion addresses and live on both clear and dark web." Klijnsma told BleepingComputer.
SSL certs help ID public IP address of dark web sites
When operators of Tor hidden services add an SSL certificate to their site, they associate the .onion domain with the certificate as shown below.
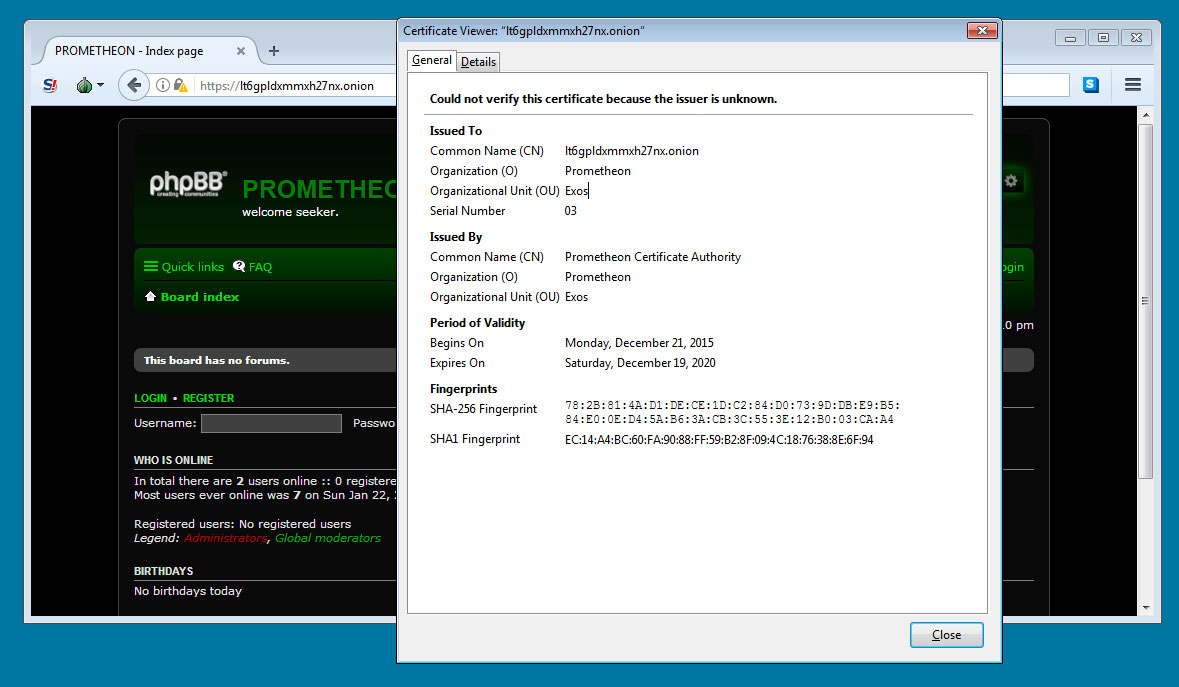
If the Tor site is misconfigured so that it listens on a public IP address, this same certificate containing the .onion domain will be used for that IP address as well. As RiskIQ crawls the Internet and catalogs all SSL certificates it finds being used by a site, it will associate this .onion certificate with the public IP address it finds it on.
This allows Klijnsma to use the RiskIQ database to easily search for .onion certificates and see what public IP address they are mapped to as shown below.
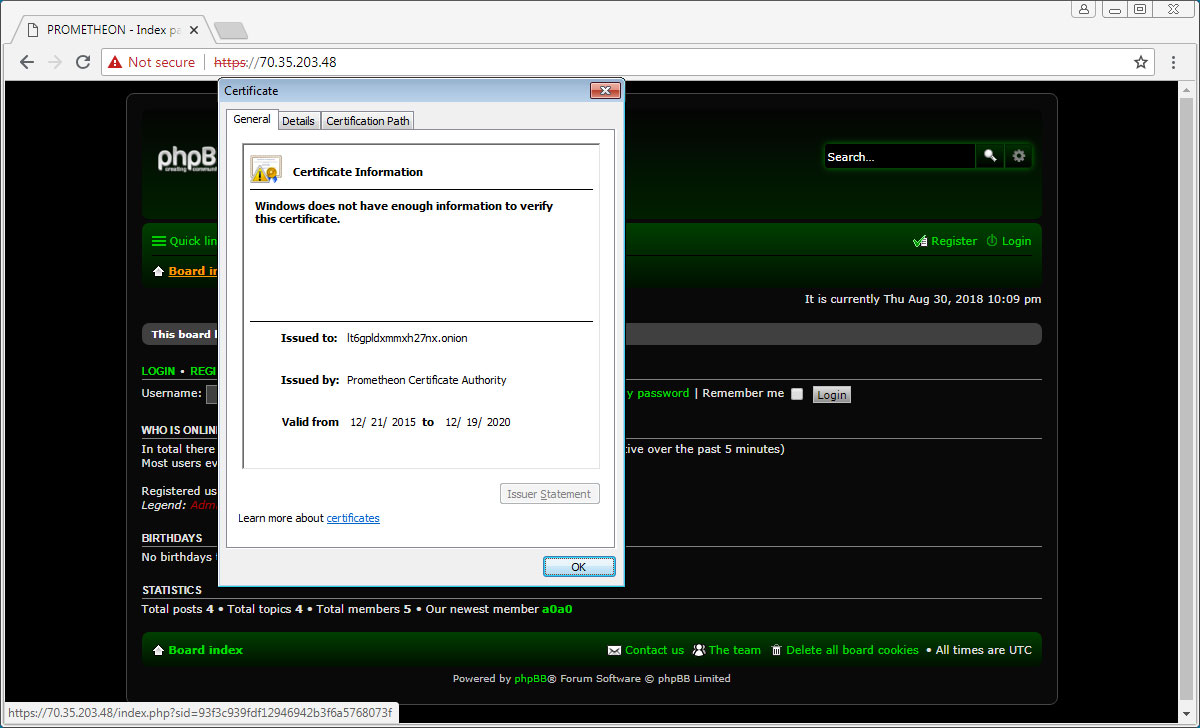
You can see how this was illustrated in a tweet by Klijnsma below.
Another #Tor hidden service exposed through an incorrect configuration of the listening server. Hiding your private forum on the deep dark (and still very public) web. Certificate can be found here (host is still live!): https://t.co/KEqN6hfyFb pic.twitter.com/cwHOuUdwmk
— Yonathan Klijnsma (@ydklijnsma) August 4, 2018
Tor users think Klijnsma is attacking Tor
Some users feel that Klijnsma's research is an attack on Tor, while the researcher says its actually the opposite. Instead of attacking Tor, Klijnsma is trying to bring to light the inherent problems associated with not properly configuring a Tor hidden service.
For those who are telling me to stop attacking #Tor, I'm not attacking Tor.
— Yonathan Klijnsma (@ydklijnsma) August 4, 2018
I'm merely trying to get across the concept that there's a difference between setting up the listening host for your server as 0.0.0.0 or * vs 127.0.0.1. https://t.co/zhY27p8Wrw
In order to protect a site from being exposed in this manner, it's quite simple according to the researcher. "They should only listen on 127.0.0.1."


Comments
battlesbc - 5 years ago
Had this very error setup on my server. It had been recommended by an expert before this security problem was found. In /postfix/main.cf,
Change: mynetworks = 127.0.0.0/8 my.ip.adr.??/32
To: mynetworks = 127.0.0.0/8
battlesbc - 5 years ago
Another suggestion that needs to be made.
Change: inet_interfaces = all
To: inet_interfaces = localhost
Restart Postfix.
PerspectiveObjective - 5 years ago
Are there not hundreds of similar instances of oooops now look at this idiot or group of the walking dead in the dark web and beyond, that are not talked about or made public? You know by slow ah special kids LOCAL authoritive groups and so called 90\/+ entities.