
Network and email security firm Barracuda says it remotely patched all active Email Security Gateway (ESG) appliances on December 21 against a zero-day bug exploited by UNC4841 Chinese hackers.
The company deployed a second wave of security updates a day later on already compromised ESG appliances where the attackers deployed SeaSpy and Saltwater malware.
Disclosed on Christmas Eve and tracked as CVE-2023-7102, the zero-day is due to a weakness in the Spreadsheet::ParseExcel third-party library used by the Amavis virus scanner running on Barracuda ESG appliances.
Attackers can exploit the flaw to execute arbitrary code on unpatched ESG appliances through parameter injection.
The company also filed the CVE-2023-7101 CVE ID to track the bug separately in the open-source library, which is still awaiting a patch.
"No action is required by customers at this time, and our investigation is ongoing," Barracuda said in an advisory issued on December 24.
"Barracuda, working in collaboration with Mandiant, assesses this activity is attributable to continued operations of the China nexus actor tracked as UNC4841.
"For organizations utilizing Spreadsheet::ParseExcel in their own products or services, we recommend reviewing CVE-2023-7101 and promptly taking necessary remediation measures."
Second wave of zero-day attacks this year
In May, the same hacker group used another zero-day (CVE-2023-2868) to target Barracuda ESG appliances as part of a cyber-espionage campaign.
Barracuda revealed the zero-day had been abused in attacks for at least seven months, since at least October 2022, to deploy previously unknown malware and exfiltrate data from compromised systems.
They deployed SeaSpy and Saltwater malware and the SeaSide malicious tool to gain remote access to hacked systems via reverse shells.
Submarine (aka DepthCharge) and Whirlpool malware was deployed in the same attacks as later-stage payloads to maintain persistence to a small number of previously compromised devices on networks of high-value targets.
The attackers' motivation was espionage, with UNC4841 hackers engaging in targeted exfiltration from breached networks to high-profile government and high-tech users.
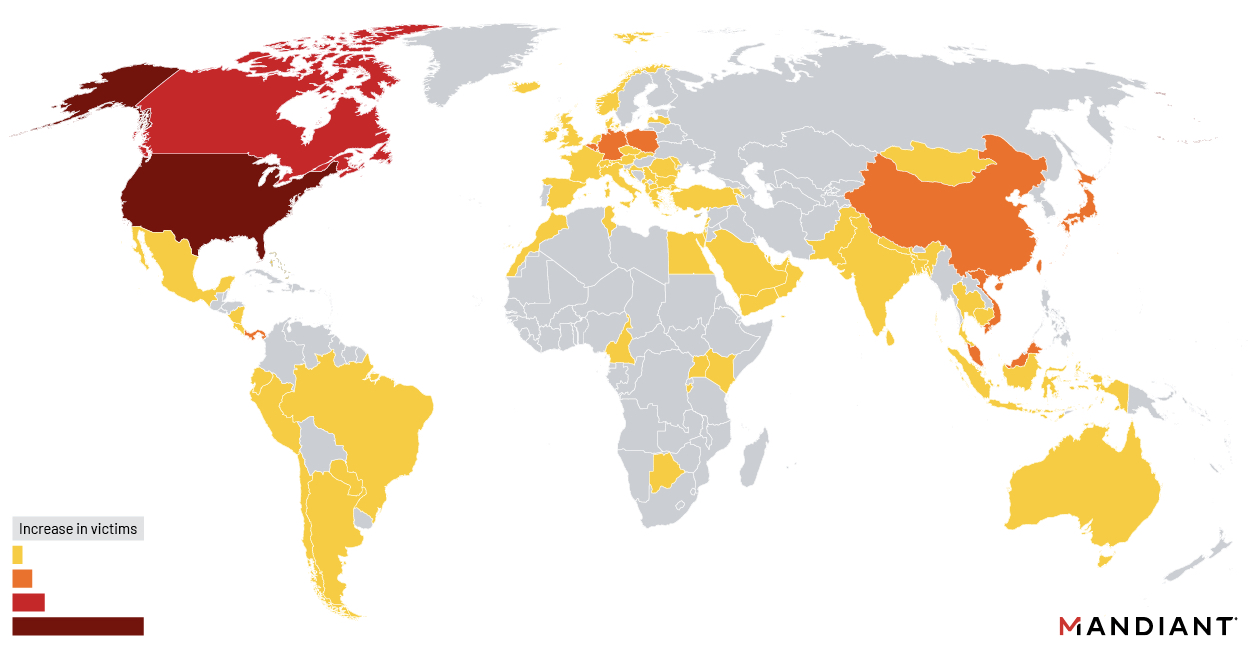
Almost a third of appliances hacked in the May campaign belonged to government agencies, most of them between October and December 2022, according to cybersecurity firm Mandiant.
Barracuda warned customers after the May attacks that they must replace all compromised appliances immediately, even those they had already patched (around 5% of all appliances were breached in the attacks).
Barracuda says more than 200,000 organizations worldwide use its products, including top companies like Samsung, Kraft Heinz, Mitsubishi, and Delta Airlines.



Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now