A new attack that uses terrestrial radio signals to hack a wide range of Smart TVs raises an unsettling prospect—the ability of hackers to take complete control of a large number of sets at once without having physical access to any of them.
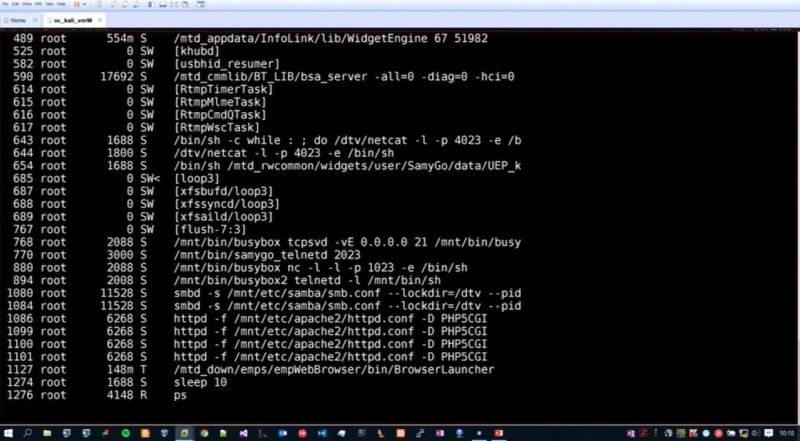
The proof-of-concept exploit uses a low-cost transmitter to embed malicious commands into a rogue TV signal. That signal is then broadcast to nearby devices. It worked against two fully updated TV models made by Samsung. By exploiting two known security flaws in the Web browsers running in the background, the attack was able to gain highly privileged root access to the TVs. By revising the attack to target similar browser bugs found in other sets, the technique would likely work on a much wider range of TVs.
"Once a hacker has control over the TV of an end user, he can harm the user in a variety of ways," Rafael Scheel, the security consultant who publicly demonstrated the attack, told Ars. "Among many others, the TV could be used to attack further devices in the home network or to spy on the user with the TV's camera and microphone."
Scheel's exploit relies on a transmitter that's based on digital video broadcasting—terrestrial, a transmission standard that's built into the vast majority of TVs. TVs that are connected to the Internet, are currently tuned to a DVB-T-based station, support the hybrid broadcast broadband TV standard, and contain at least one critical vulnerability that can be exploited without showing any outward signs anything is amiss.
The exploit, which Scheel developed for Swiss security consulting company Oneconsult, was demonstrated in February at the European Broadcasting Union Media Cyber Security Seminar. Once completed, the attack gave Scheel the ability to remotely connect to the TV over the Internet using interfaces that allowed him to take complete control of the device. The infection was also able to survive both device reboots and factory resets. A recording of the talk is available below:
Scheel's approach, by contrast, can work against many TVs at once and eliminates the need for the attacker to physically control the device. Instead, the hacker need only turn on a transmitter that's within range of a large number of sets, say, in a densely populated apartment building or from a balcony that's near a TV of interest. The approach could also be modified in ways that give it greater reach. For instance, in the event a TV station or network was compromised—for example, a more extreme version of the 2015 hack that blacked out 11 channels belonging to French broadcaster TVMonde5—the attackers could surreptitiously embed malicious code into the signal being broadcast to millions of TVs. Embedding malicious commands into broadcasts from cable or satellite providers is also theoretically possible. A 2014 research paper written by Yossef Oren and Angelos D. Keromytis discussed embedding the exploits into various types of broadcasts.
The hacks underscore the risks of so-called "Internet of Things" devices, the vast majority of which are given network access and computing functionalities without being adequately secured. TVs and other Internet-connected appliances almost universally lack application sandboxing and other exploit mitigations that are a standard part of computer and mobile operating systems. Even worse, most devices run old versions of Linux and open source browsers that contain critical vulnerabilities. While patches are generally available on the Internet for the individual components, manufacturers rarely give customers a way to install them on the devices in a timely way.
Oren, one of the authors of the 2014 paper, told Ars:
This research is significant because TVs are used by a fundamentally different demographic than computers. People who use TVs don't know/care about security, they aren't used to getting security prompts from their TVs, they don't have the discipline of installing security updates, and so on.
Listing image by Samsung Newsroom
reader comments
139