
Researchers from Cisco Talos working with the Dutch police obtained a decryption tool for the Tortilla variant of Babuk ransomware and shared intelligence that led to the arrest of the ransomware's operator.
Tortilla is a Babuk ransomware variant that emerged in the wild shortly after the source code of the original malware leaked on a hacker forum.
The threat actor behind it has been targeting Microsoft Exchange servers with ProxyShell exploits to deploy the data-encrypting malware.
Avast released a decrypter for Babuk a month before the new variant appeared but it didn't work for Tortilla encryption because it used a different private key.
Tortilla unlocked
Today, Cisco Talos announced that, in cooperation with the Dutch police, it obtained a decryptor that the Tortilla ransomware operator provided to victims that paid the ransom.
Acting on threat intelligence from Cisco Talos, law enforcement authorities were able to identify and arrest in Amsterdam the threat actor behind the Tortilla ransomware operation.
According to the researchers, the executable contained a single public/private key pair that was used in all attacks. After extracting the key, the analysts shared it with Avast to update their Babuk decryptor.
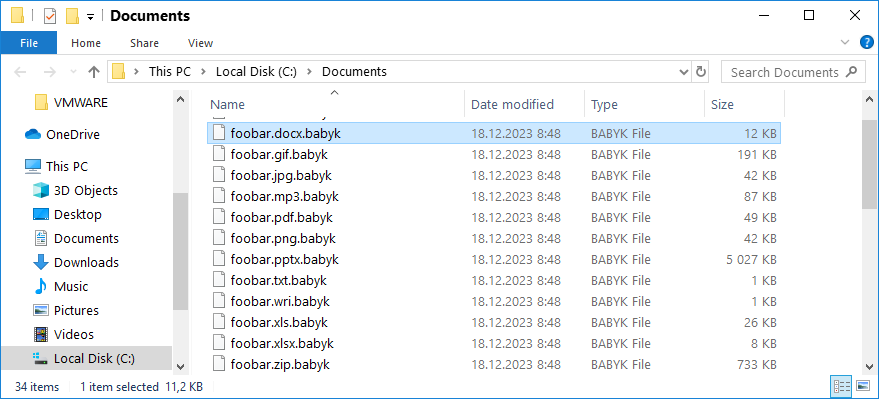
Avast added the Tortilla decryption key to the Babuk decryptor's fourteen ECDH-25519 keys that were obtained from the 2021 source code leak.
Victims of the Babuk variant can download Avast's generic decryption tool for free from here.
Cisco Talos notes that Tortilla is not the only operation that used Babuk ransomware code to encrypt victims. Since December 2021, seven other operations emerged: Rook, Night Sky, Pandora, Nokoyawa Cheerscrypt, AstraLocker 2.0, ESCiArgs, Rorschach, RTM Locker, and the RA Group.


Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now